What Are the Frequently Encountered E-Commerce Fraud Varieties?
5. Refund Fraud
“Trust takes years to build, seconds to break, and forever to repair.” – Dhar Mann
Navigating the treacherous waters of e-commerce fraud can feel like an epic quest, as you shield your digital domain from the cunning foes of online deception. As we unveil the dastardly adversaries in our e-commerce chronicles, you’ll be better equipped to defend your realm.
1. Credit Card Fraud

In the vast, cybernetic savannah of e-commerce, there’s a beast of burden that we all must be wary of – the notorious and insidious Credit Card Fraud. This dastardly digital menace can take many forms, and today, we’re going to venture deep into its lair. Buckle up, dear readers, as we journey through the treacherous terrain of this digital demon!
True Card Fraud
First on our list of malevolent machinations, we have the ever-classic “True Card Fraud.” This is where the fraudster gets their grubby digital mitts on your actual credit card information. Picture it like a pickpocket in a crowded cyber marketplace, swiping your card details instead of your wallet. They use your hard-earned money to go on a shopping spree, while you’re left wondering why your card is suddenly buying vintage sneakers at 3 am!
Card Testing Fraud
Next up, we’ve got the sly fox of fraud: Card Testing. Imagine this – you’re an unsuspecting merchant, and an order pops up. Nothing suspicious, right? Wrong! In the blink of an eye, hundreds of small transactions start flooding in. This is a fraudster, testing stolen card details to see if they work before going for the big-ticket items. It’s like a game of whack-a-mole, but you’re the mole, and the hammer is a wave of fraudulent transactions!
Friendly Fraud
Don’t let the name fool you, there’s nothing friendly about “Friendly Fraud.” This crafty scam is where the customer makes a purchase, receives the goods, then files a chargeback with their bank, claiming they never received the item. It’s like inviting someone over for dinner, only for them to steal your silverware and then complain about the food!
In the cyber jungle of e-commerce, credit card fraudsters are prowling, looking for their next unsuspecting victim. But fear not, intrepid e-commerce explorer! Forewarned is forearmed. Stay savvy, stay smart, and most importantly, stay safe out there in the digital wilds!
2. Identity Theft Fraud
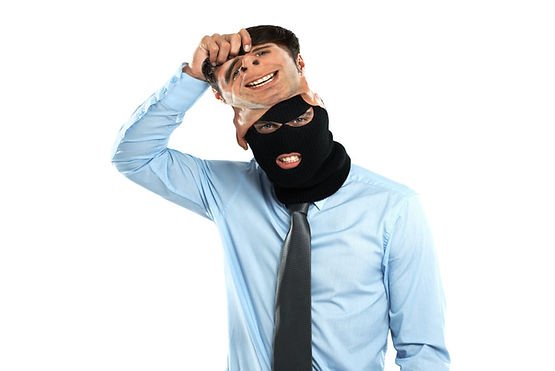
Prepare to embark on a journey into the shadowy world of online identity theft. Picture it as the digital equivalent of body snatchers, only instead of taking over your physical form, they’re after your personal and financial information. Get ready to explore the mysterious, murky underbelly of e-commerce fraud in our next thrilling episode!
Phishing Attacks
First, we cast our nets into the turbulent seas of “Phishing Attacks.” This is the “old faithful” of online scams. Fraudsters send out deceptive emails, pretending to be your bank, your favorite online store, or even your grandmother asking for your login details. It’s like getting a letter from the tooth fairy, only instead of leaving a dollar under your pillow, she empties your bank account!
Account Takeover
Next, we plunge into the ominous depths of “Account Takeover.” In this scenario, fraudsters use leaked or stolen data to gain access to your e-commerce accounts. They change your login details, lock you out, and then run amok with your credit card. Think of it as a digital home invasion – your e-commerce account is the house, and the fraudster is the unwelcome guest raiding your fridge and maxing out your credit card on pay-per-view!
Synthetic Identity Fraud
As we delve deeper, we encounter the cybernetic chimera known as “Synthetic Identity Fraud.” Here, fraudsters don’t just steal an identity; they create a new one by blending real and fake information. It’s like Dr. Frankenstein in the digital age, building a monster out of stolen Social Security numbers, fake names, and invented addresses!
Man-in-the-Middle Attacks
Finally, we meet the ultimate puppeteer of identity theft: the “Man-in-the-Middle Attack.” This method involves a fraudster secretly intercepting and possibly altering the communication between two parties to steal data. Imagine you’re passing notes in class, but there’s a sneaky classmate in between reading and rewriting your messages. That’s a man-in-the-middle attack for you!
The online world might seem like a scary place, with digital boogeymen lurking around every corner. But remember, knowledge is power. So, suit up, stay vigilant, and keep your virtual sword ready to combat the dragons of identity theft in the e-commerce realm!
3. Chargeback Fraud

Ah, the fickle and frustrating world of Chargeback Fraud! It’s like a game of tug-of-war, only instead of a rope, there’s money at stake, and the players can sometimes be less than fair. It’s a complex labyrinth of disputed transactions and ill-gotten gains. So, hold on to your hats, dear readers, as we navigate the twists and turns of this e-commerce enigma!
Friendly Fraud
First, we have the return of an old ‘friend’—the misnamed, mischievous “Friendly Fraud.” It’s like a magic show where the magician disappears with your money! Here, a customer makes a purchase, receives the goods, then declares to their bank they never got the item or didn’t authorize the purchase. Voila, the money reappears in their account, leaving the merchant in the lurch!
Chargeback Laundering
Next, we delve into the shadowy underworld of “Chargeback Laundering.” It’s the money laundering of the digital age! Fraudsters use stolen credit card information to make purchases, then the ‘real’ cardholder disputes the transaction. The result? The money gets washed clean back to the fraudster, leaving the merchant high and dry!
Affiliate Fraud
Now, let’s turn our attention to the sly fox of chargeback fraud: “Affiliate Fraud.” In this scenario, affiliates, eager to earn a commission, generate fraudulent sales, leading to an increase in chargebacks. It’s like having a double agent in your sales team, making deals that end up costing you money!
Serial Chargeback Fraud
Last, but not least, we encounter the relentless beast of “Serial Chargeback Fraud.” This involves customers who habitually dispute transactions, causing a nightmare for businesses. Imagine a repeat offender, a serial movie returner if you will, only instead of DVDs, they’re returning digital purchases and causing a logistical horror show!
So, there you have it, the wild west of e-commerce fraud. It might seem like a daunting landscape, but remember, knowledge is the best defense. Keep your eyes open, your wits about you, and don’t let the chargeback fraudsters get the best of you in this e-commerce showdown!
4. Account Takeover Fraud

Ladies and Gentlemen, allow me to introduce you to the high-tech heist of the e-commerce world – Account Takeover Fraud. Imagine your e-commerce account as a digital penthouse, with a view of your personal and financial data. Now, picture a fraudster as a sophisticated burglar, bypassing security, and throwing a party in your absence. Let’s delve into the various ways they manage to pull off this audacious stunt!
Phishing
First up in our rogues’ gallery, we have the artful dodger of cybercrime – “Phishing.” In this classic trick, fraudsters send you an email masquerading as a trusted entity, baiting you to reveal your login credentials. It’s like a game of hide-and-seek, except you’re unwittingly hiding your details where fraudsters seek them!
Credential Stuffing
Next, we have “Credential Stuffing.” In this method, fraudsters use stolen or leaked username-password combinations on multiple websites, hoping that you’ve reused credentials. It’s like trying every key on a giant keyring until they find the one that opens your digital front door!
Malware
Here’s where things get a bit more sinister with “Malware.” This involves malicious software installed on your device without your knowledge, tracking your keystrokes, and transmitting your login details back to the fraudster. Imagine a tiny digital spy hiding in your computer, reporting back on your every move!
Social Engineering
Finally, we have “Social Engineering.” This isn’t about building digital bridges or cyber skyscrapers; instead, it’s about manipulating people into giving up their account details. Think of it as the con artist of the cyber world, sweet-talking you into handing over the keys to your e-commerce account!
Account Takeover Fraud might sound like something out of a high-tech thriller, but it’s a real and present danger in the world of e-commerce. But fear not! Armed with knowledge, you can keep your accounts locked down tighter than Fort Knox. Stay alert, stay safe, and keep those cyber burglars at bay!
5. Refund Fraud

Welcome, dear readers, to the grand masquerade of the e-commerce world, the shapeshifter known as Refund Fraud. Picture a masquerade ball where attendees, draped in the cloak of deceit, dance around, feigning innocence while emptying the coffers. Let’s unmask the various guises of this audacious scam!
Return to Sender
Kicking off our parade of pretenders, we have the “Return to Sender” ploy. In this act, the customer claims to have returned the product but sends an empty package. It’s like getting a beautifully wrapped gift, only to find it’s filled with disappointment and lost profits!
Wardrobing
Next, we introduce you to the deceptive dance of “Wardrobing.” Customers buy products, use them for a short time, and then return them for a full refund. Imagine having a guest over who uses your guest towels and then stuffs them back into the linen closet!
Friendly Fraud
Once again, we encounter the ironically named “Friendly Fraud.” In this scenario, a customer requests a refund, claiming they never received the product, even though they did. It’s like claiming you never got an invitation to the party, despite being caught on camera doing the Macarena!
Price Arbitrage
Finally, we unveil the chameleon of refund frauds – “Price Arbitrage.” Here, customers buy discounted products and return them to another store selling the same product at a higher price. It’s like buying an apple for a dollar at the farmer’s market and selling it for two at a gourmet grocery store!
The ballroom of e-commerce can sometimes seem filled with masked marauders, all dancing the dance of Refund Fraud. But with the right knowledge and a discerning eye, you can unmask these fraudsters and keep your business secure. So, keep your eyes peeled and your guard up as you waltz through the wonderful world of e-commerce!
6. Phishing Fraud

Welcome to the dark, underwater world of Phishing, where fraudsters are the anglerfish, and you, dear reader, are the unsuspecting prey. These predators use the lure of familiarity to hook you into their schemes. Let’s dive deeper into the murky waters and explore the various forms of this e-commerce fraud!
Email Phishing
First up in our underwater exploration, we encounter “Email Phishing.” It’s the Great White Shark of this digital ocean. Fraudsters send out deceptive emails, pretending to be reputable companies, hoping to trick you into revealing sensitive information. It’s like getting a letter from a long-lost relative who suddenly needs your bank details to share their fortune!
Spear Phishing
Next, we navigate the depths to meet the deadly “Spear Phishing.” Unlike its cousin Email Phishing, this method targets specific individuals or companies. It’s like a sniper in the underwater world, using precision and detailed information to hit its mark!
Whaling
Then, we have “Whaling,” the Moby Dick of phishing attacks. Here, the big fish—CEOs and high-ranking officials—are the targets. Imagine a fraudulent email disguised as a legal subpoena, financial claim, or executive issue, aimed at harpooning these whales!
Smishing and Vishing
Finally, we surface to encounter the twin terrors of “Smishing” and “Vishing.” These methods use SMS and voice calls, respectively, to trick victims into giving up personal information. It’s like getting a call or a text from a beloved celebrity, only to discover it’s a fraudster in disguise!
The world of phishing may seem deep and full of terrors, but fear not! Knowledge is your lifeboat in this treacherous sea. So, keep your wits about you, and don’t take the bait! Always remember: when something smells fishy, it probably is. Stay safe on your e-commerce voyage!
7. Triangulation Fraud

Step right up, folks, as we unpack the fascinating spectacle of Triangulation Fraud! This act isn’t as simple as a one-two punch; it’s a three-ring circus of deceit, making it one of the more complex and cunning scams in the e-commerce big top.
The Fraudulent Storefront
In the first ring of this cyber circus, we have the “Fraudulent Storefront.” Here, the scam artist sets up a fake online store offering high-demand goods at unbelievably low prices. It’s like a magician promising to pull a rabbit out of a hat for a nickel!
The Unsuspecting Customer
In the second ring, enter the “Unsuspecting Customer.” Drawn by the allure of a great deal, they place an order at the fraudulent store. It’s akin to the thrill of seeing a two-headed lion, only to realize later it was just a trick of the light!
The Legitimate Purchase
Finally, in the third ring, we witness the “Legitimate Purchase.” The fraudster uses stolen credit card information to buy the ordered item from a legitimate e-commerce store and ships it to the unsuspecting customer. It’s as if our magician, instead of pulling a rabbit out of the hat, makes your wallet disappear!
The Triangulation Fraud Act can be a hard one to spot in the e-commerce circus. The illusion is elaborate, the misdirection is cunning, and the trickery is top-notch. But remember, folks, the amazing world of e-commerce doesn’t have to be a house of mirrors. Keep your eyes open, question the too-good-to-be-true, and you’ll navigate this circus-like a true ringmaster!
How to Safeguard Your E-Commerce Business from Fraud?
Fear not, noble e-commerce warrior, for we also present you with a formidable arsenal to safeguard your online kingdom against these nefarious foes:
1. Use a secure payment gateway
2. Implement two-factor authentication
6. Chargeback protection services
1. Use a Secure Payment Gateway

Imagine navigating the treacherous seas of e-commerce, with fraudsters lurking like pirates, ready to plunder your treasure. Your first line of defense? A robust, secure payment gateway, serving as your trusty galleon, guiding you safely through these potentially perilous waters!
Encryption
Firstly, make sure your payment gateway is armed with top-tier “Encryption.” Think of it as the impenetrable hull of your ship, ensuring that your customer’s sensitive data can navigate the open waters without falling into pirate hands.
Two-Factor Authentication
Next, equip your vessel with “Two-Factor Authentication.” It’s like having a loyal parrot that squawks a secret code, ensuring that only the rightful captain can steer the ship and approve transactions.
PCI DSS Compliance
Finally, your payment gateway should be “PCI DSS Compliant.” This is the gold standard in payment security, akin to flying the Jolly Roger of respectability, showing all that you mean business and won’t be easily boarded.
Navigating the e-commerce seas doesn’t have to be a pirate-infested nightmare. With a secure payment gateway, you can sail confidently, knowing you’re well-equipped to fend off any fraudsters that dare cross your path. So, hoist the mainsail, secure the treasure, and chart a course for e-commerce success!
2. Implement Two-Factor Authentication

Enter the world of e-commerce security, where Two-Factor Authentication (2FA) is the superhero, swooping in to save the day from potential fraudsters. Picture 2FA as a super-powered gatekeeper, requiring more than just a simple password to unlock the gate to your e-commerce empire. Let’s take a look at how this superhero operates!
Something You Know
Our hero’s first power is the “Something You Know” factor. This usually takes the form of a password or a PIN. Imagine it as the secret handshake you share with your superhero, a handshake only you know and can execute perfectly!
Something You Have
Next, we have the “Something You Have” factor. This could be a device like your smartphone or a hardware token. Think of it as a special gadget from our superhero’s utility belt, something you always have at hand to battle potential fraudsters!
Something You Are
Finally, there’s the “Something You Are” factor. This involves biometrics like fingerprints or facial recognition. Envision it as your superhero’s unique identity, as distinct and identifiable as a superhero emblem!
Implementing 2FA for your e-commerce business is like forming a dynamic duo with this security superhero. Together, you’ll be prepared to thwart any villainous attempts to breach your defenses. So, suit up, stay vigilant, and keep your e-commerce city safe from the clutches of e-commerce fraudsters!
3. Use SSL Certificates

Ladies and gentlemen, step right up and witness the magic of SSL Certificates! These aren’t your typical rabbits-out-of-hats tricks; these are the real-deal security enchantments for your e-commerce platform. Picture an SSL Certificate as your magic cloak, rendering your sensitive data invisible to the prying eyes of internet tricksters!
Encryption
The first spell in our SSL grimoire is “Encryption.” This mystical incantation turns your customer’s data into a cryptic puzzle that only the intended recipient can solve. It’s like whispering a secret in an indecipherable language, safe from eavesdroppers!
Authentication
Next up, we have the spell of “Authentication.” This magic verifies the identities of communicating parties, making sure your customers are dealing with the real wizard – that’s you, not an impostor. Imagine a magical mirror that reflects only the true image of the person standing in front of it!
Trust
Finally, there’s the enchantment of “Trust.” An SSL Certificate shows customers that your site is secure, which increases their trust in your e-commerce platform. It’s akin to the Wizard’s seal of approval, reassuring everyone that your magical marketplace is safe for business!
Incorporating SSL Certificates into your e-commerce platform is like adding powerful spells to your wizarding repertoire. With these enchantments, you’ll keep your business safe from the dark arts of e-commerce fraud. So, grab your wand, cast these spells, and let the magic of safe e-commerce unfold!
4. Educate Customers

Welcome to Fraud Prevention 101, where customers are students, and you, the e-commerce site owner, are the professor. The syllabus? How to spot and avoid potential fraud. Let’s take a roll call of the crucial lessons that your e-commerce university should impart!
Recognizing Secure Websites
First, on the curriculum, we have “Recognizing Secure Websites.” It’s like teaching your students how to differentiate between a Van Gogh and a forgery. Show them the signs of a secure site, like the HTTPS in the URL and the padlock icon.
Secure Personal Information
Next up, we delve into “Secure Personal Information.” Teach them the importance of strong, unique passwords, akin to creating an unbreakable secret code. Encourage them to change these passwords frequently, like changing disguises in a spy movie!
Safe Online Shopping Practices
Our final lesson is on “Safe Online Shopping Practices.” Educate them on the red flags of fraud, such as too-good-to-be-true deals or requests for unusual payment methods. It’s like teaching them to spot a wolf in sheep’s clothing!
When it comes to preventing e-commerce fraud, knowledge is power. By educating your customers, you empower them to help keep your e-commerce platform safe. So, dust off that chalkboard, prepare your lesson plans, and let’s educate to eradicate e-commerce fraud!
5. Track IP Addresses

In the digital game of hide-and-seek that is e-commerce, IP addresses are your secret weapon. Think of tracking IP addresses like tracking footprints in a forest; they can lead you straight to your elusive target, helping you uncover any potential fraudsters lurking in the shadows!
Identify Unusual Activity
Firstly, tracking IP addresses can help you “Identify Unusual Activity.” Is there a sudden flurry of transactions from a single IP address? That’s akin to finding a cluster of fresh footprints around a treasure chest. It might be a sign of a fraudster on a spree!
Spot Geographical Inconsistencies
Next, this practice can help you “Spot Geographical Inconsistencies.” If a customer’s billing address is in New York, but the IP address is in Timbuktu, it’s like spotting the footprints of a polar bear in the Sahara. Something doesn’t add up!
Blacklist Suspicious IPs
Finally, by tracking IP addresses, you can “Blacklist Suspicious IPs.” If an IP address has been associated with fraudulent activity, ban it from your site. It’s like setting a trap for that polar bear that’s been leaving footprints!
In the vast digital forest of e-commerce, tracking IP addresses can help you stay one step ahead of potential fraudsters. So, grab your digital magnifying glass and start tracking those cyber footprints to safeguard your e-commerce platform!
6. Chargeback Protection Services

In the epic saga of e-commerce, chargeback protection services are your trusty knights in shining armor, ready to defend your kingdom against the dragon of fraud. Let’s raise the drawbridge and explore the castle to keep where these gallant guardians hold the line!
Preventive Measures
First up, these knights employ “Preventive Measures.” They examine every transaction, scrutinizing it as a royal advisor might a strategic battle plan. They look for signs of fraud, such as mismatched addresses or suspiciously large orders.
Alerts
Next, chargeback protection services provide “Alerts.” It’s like having a vigilant watchtower guard who signals at the first sign of an invading army – in this case, suspicious transactions or potential chargebacks.
Dispute Management
Finally, they offer “Dispute Management.” Should a chargeback occur, they will fight on your behalf, wielding their expertise like a knight’s sword to help win the dispute. It’s akin to having a champion in a medieval joust!
In the battlefield of e-commerce, chargeback protection services can be your stalwart defender against the onslaught of fraud. With their shield raised and sword drawn, they stand ready to protect your kingdom. So, sound the trumpets, let the banners fly, and let your defenders do what they do best!
7. Fraud Detection Software

Imagine a cybernetic sentinel, tirelessly scanning the horizons of your e-commerce platform for any signs of fraud. That’s fraud detection software for you, a futuristic guardian equipped with advanced algorithms and machine learning. Let’s dive into the three core protocols of this digital watchman!
Real-Time Scanning
First up, we have “Real-Time Scanning.” This protocol is always active, continuously monitoring your transactions like a hawk soaring above its territory. It detects and flags unusual behavior instantly, faster than a cyborg cheetah on roller skates!
Machine Learning
Next, “Machine Learning” enables the software to learn from past transactions, identifying patterns and trends in fraudulent activities. It’s as if our cyber sentinel can predict the future, foreseeing potential threats before they happen!
Customizable Rules
Finally, “Customizable Rules” allow you to fine-tune the software according to your specific needs. You set the parameters, and the software scans accordingly, like programming a robot butler to serve only your favorite snacks!
In the digital landscape of e-commerce, fraud detection software stands as a sentinel, ever-watchful, and ready to protect. So, power up your cyber guardian, set it on patrol, and rest easy knowing that your e-commerce platform is under the watchful eyes of advanced technology!
8. Monitor Transactions

Step into the role of a digital Sherlock Holmes, meticulously investigating each transaction on your e-commerce platform for signs of fraud. Monitoring transactions is like piecing together a puzzle, looking for any inconsistencies or anomalies that might reveal a fraudulent plot. Let’s don our deerstalker hats and delve into the key aspects of this investigative process!
Unusual Purchasing Patterns
First, keep an eye out for “Unusual Purchasing Patterns.” If a customer who usually buys a single t-shirt suddenly orders fifty, it’s like finding a footprint at a crime scene. Something might be afoot!
Multiple Failed Payment Attempts
Next, “Multiple Failed Payment Attempts” can be a red flag. It’s as if someone is trying to pick a lock, unsuccessfully. If you see this happening, it’s time to step in and investigate.
Discrepancies in Billing and Shipping Addresses
Lastly, “Discrepancies in Billing and Shipping Addresses” should raise your detective’s intuition. It’s like a suspect having an alibi that doesn’t quite add up. If the billing and shipping addresses are miles apart, it might be time to shine a light on the case.
Monitoring transactions is like playing detective, keeping your e-commerce platform safe from fraud. So, dust off your magnifying glass, polish your deduction skills, and let’s solve the mystery of e-commerce fraud prevention together!
9. Use CVV and AVS Checks

In the grand theatre of e-commerce, CVV and AVS checks are your trusty doormen, ensuring only the right patrons gain entry. Like diligent bouncers, they check the credentials of every transaction, adding a sturdy layer of security to your online business. Let’s take a closer look at these stalwart protectors!
Card Verification Value (CVV)
First, we have the “Card Verification Value (CVV).” This is a 3 or 4-digit code on the back of a credit card, serving as a secret handshake between the customer and the e-commerce site. Without it, no entry! If a transaction fails the CVV check, it’s like someone trying to sneak into the theatre with a counterfeit ticket.
Address Verification Service (AVS)
Next up is the “Address Verification Service (AVS).” This system checks if the billing address entered by the customer matches the one registered with the credit card company. If they don’t match, it’s as if someone is trying to use a stolen VIP pass. Access denied!
Using CVV and AVS checks is like having a couple of experienced bouncers guarding the entrance to your e-commerce platform. So, let them do their job, and enjoy the show knowing that your online business is in safe hands! And while you’re at it, why not consider adding a touch of panache to your e-commerce playbook? Our expert e-commerce coaching services could be your virtuoso conductor, orchestrating your business’s success with flair and finesse. Reach out to us and let’s make your online performance a standing ovation-worthy affair!

